Trezor — Start
The Trezor start moment is the small, deliberate interaction that bridges offline custody with online functionality. It is where human intent meets cryptographic authority: you connect, verify, and confirm — and the device signs only what you approve. This page explains how that interaction works, what makes it secure, and how to shape a robust workflow for everyday and high-value operations.
Custody by Design
Private keys never leave Trezor hardware. The start flow unlocks a local signing interface while preserving isolation: the host receives signatures, not secrets. Treat every signature request as a contract that requires your explicit approval.
Human Verification
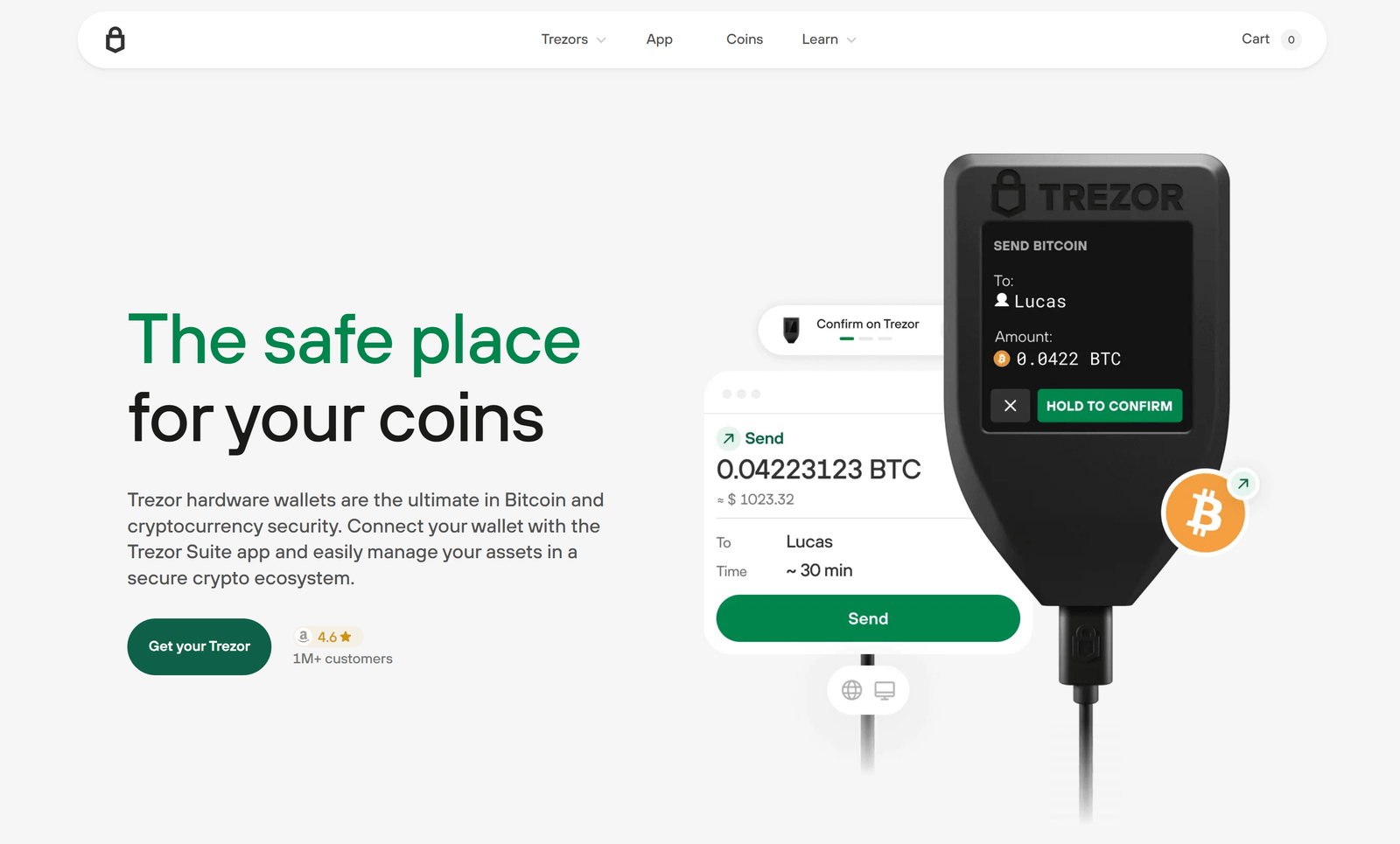
At startup and for every signature, Trezor displays clear transaction metadata. Confirm addresses, amounts, and contract data on-device — visual confirmation is the final authority before any change to your holdings.
Trusted Hosts & Minimal Surface
Start only on machines you control. Keep your companion apps and bridge services updated, reduce extraneous plugins, and prefer air-gapped workflows for very large or automated transfers.
Practical Start Workflow
A recommended startup routine: verify firmware integrity, attach the device, confirm the session log, and only then proceed to sign. When automating, prepare transactions offline, transport to a signing host, and broadcast signed payloads from a separate, networked machine.
Recovery & Updates
Store your recovery seed offline and air-gapped. Apply firmware updates from official channels and verify signatures. A controlled, auditable update process reduces risk at each start.
Environment
Prefer private networks and trustworthy USB connections. Avoid public terminals and unknown hubs. Use hardware-based PINs and optional passphrases for added layers of protection.
The Trezor start is a brief moment with outsized importance. Treat it as a checkpoint: verify everything displayed, keep recovery material offline, and rely on the device as the single source of truth for approvals. Do this consistently, and your hardware wallet becomes the strongest link in your digital security chain.